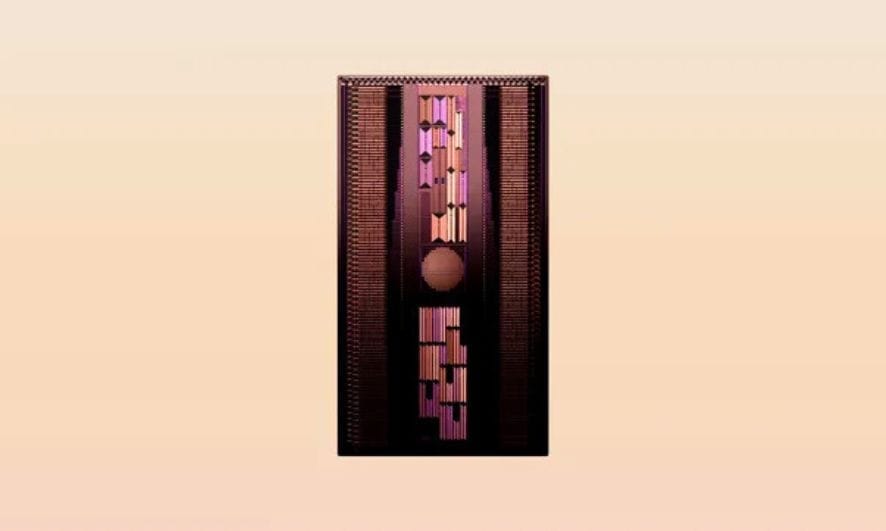
Four Zero-Day Vulnerabilities in Qualcomm Chips Put Billions of Users at Risk
Qualcomm, a global semiconductor giant, recently disclosed four zero-day vulnerabilities in its chips that are used in billions of smartphones and other devices around the world. The vulnerabilities, which have been exploited in limited, targeted attacks, could allow attackers to take control of affected devices or steal sensitive data. This October, Qualcomm addressed 21 vulnerabilities in its security advisories.

The four vulnerabilities are:
- CVE-2023-33106: A use-after-free vulnerability in the Adreno GPU driver
- CVE-2023-33107: A use-after-free vulnerability in the Compute DSP driver
- CVE-2022-22071: A possible use-after-free vulnerability in Snapdragon Auto, Snapdragon Compute, Snapdragon Connectivity, Snapdragon Consumer IOT, Snapdragon Industrial IOT, Snapdragon Mobile, Snapdragon Voice & Music
- CVE-2023-33063: A buffer copy without checking the size of input vulnerability in the WLAN firmware
“There are indications from Google Threat Analysis Group and Google Project Zero that CVE-2023-33106, CVE-2023-33107, CVE-2022-22071, and CVE-2023-33063 may be under limited, targeted exploitation,” Qualcomm wrote in its security advisory.
Beyond the zero-days, three other critical vulnerabilities have come to the fore:
- CVE-2023-24855: With a CVSS score of 9.8, this vulnerability pertains to memory corruption in the Modem while processing security-related configurations. This has wide-ranging implications, as an extensive list of chipsets, including the Snapdragon 888, 865, and 855, among others, are affected.
- CVE-2023-28540: Rated at a CVSS score of 9.1, this vulnerability is tied to a cryptographic issue due to improper authentication during a TLS handshake in the Data Modem. The expansive list of affected chipsets includes the likes of Snapdragon 888, 865, 855, and many others.
- CVE-2023-33028: Matching CVE-2023-24855 with a CVSS score of 9.8, this flaw concerns memory corruption in the WLAN Firmware during specific memory copy processes. A plethora of chipsets, including various Snapdragon platforms, are susceptible to this vulnerability.
The impact of these vulnerabilities is significant. Qualcomm chips are used in a wide variety of devices, including smartphones, tablets, laptops, routers, and cars. If an attacker is able to exploit one of these vulnerabilities, they could take control of the affected device, steal sensitive data, or even install malware.
This is especially concerning for smartphones, which contain a wealth of personal and financial information. If an attacker is able to gain control of a smartphone, they could access the user’s contacts, messages, emails, photos, and financial accounts.
Qualcomm has released patches for the vulnerabilities and urged OEMs to deploy them as soon as possible. However, until the patches are widely deployed, users of affected devices are at risk.